Azure VMware Solution Interactive demos
See AVS in action. 👀 Try these interactive demos to see real-world VMware migration use cases — complete with guided scenarios for data center exit, modernization, and hybrid management. @Microsoft Azure
See AVS in action. 👀 Try these interactive demos to see real-world VMware migration use cases — complete with guided scenarios for data center exit, modernization, and hybrid management. @Microsoft Azure
Building a Zero Trust foundation is critical for today’s cybersecurity challenges. 🛡️
Microsoft Security’s approach combines AI insights with a robust framework to help you protect your assets and users.
Discover how to implement a resilient security strategy by downloading the whitepaper. @Microsoft Security

Cyberattacks on SMBs are on the rise — is your security strategy ready? 🔒 Download the infographic to see how moving to @Microsoft Azure helps strengthen defenses, minimize risk, and build long-term resilience.
For personalized guidance on making the switch, message us to set up a consultation.

IT storms don’t wait — and neither should your strategy. ⚡
Power surges and outages can cause mission-critical downtime, but @Vertiv’s UPS, PDUs, and cloud-based monitoring help keep IT running when it matters most.
View this flyer for a breakdown of the essential tools for preparing your environment before the next blackout.
The way cybercriminals operate has fundamentally changed. The eSentire’s 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality” reveals how identity-based attacks have surged 156% since 2023, now representing nearly 60% of all confirmed threat cases.
Powered by Cybercrime-as-a-Service models, these attacks leverage Phishing-as-a-Service platforms like Tycoon2FA to bypass multi-factor authentication and gain rapid access to business email accounts and sensitive data.
Download your complimentary copy of the report for expert insight on:
-Rapid evolution of phishing and infostealer malware that turn stolen credentials into profitable identity marketplaces
-Exploitation of unmonitored endpoints and shadow IT for ransomware deployment
-Strategic recommendations for building a Zero Trust identity architecture and implementing phish-resistant authentication
DM me to discover how Mowry International can help you reduce your exposure to ident
Organizations with successful hybrid and remote work programs have seen a need for a collaboration solution that makes meetings more personalized, intelligent and protected. What are you looking for in next-gen software? Look at this blog to find out about the advantages of @Microsoft Teams Premium, the collaboration solution with enhanced features to make Teams meetings even more personalized, intelligent and protected.
The way cybercriminals operate has fundamentally changed. The eSentire’s 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality” reveals how identity-based attacks have surged 156% since 2023, now representing nearly 60% of all confirmed threat cases.
Powered by Cybercrime-as-a-Service models, these attacks leverage Phishing-as-a-Service platforms like Tycoon2FA to bypass multi-factor authentication and gain rapid access to business email accounts and sensitive data.
Download your complimentary copy of the report for expert insight on:
-Rapid evolution of phishing and infostealer malware that turn stolen credentials into profitable identity marketplaces
-Exploitation of unmonitored endpoints and shadow IT for ransomware deployment
-Strategic recommendations for building a Zero Trust identity architecture and implementing phish-resistant authentication
DM me to discover how Mowry International can help you reduce your exposure to ident

When it comes to MDR, not all solutions are created equal.
eSentire’s human-led, technology-driven approach ensures real-time threat detection and containment, providing comprehensive protection that your business can rely on. 💡
Download this datasheet to find out why @eSentire is the preferred choice for MDR.

The way cybercriminals operate has fundamentally changed. The eSentire’s 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality” reveals how identity-based attacks have surged 156% since 2023, now representing nearly 60% of all confirmed threat cases.
Powered by Cybercrime-as-a-Service models, these attacks leverage Phishing-as-a-Service platforms like Tycoon2FA to bypass multi-factor authentication and gain rapid access to business email accounts and sensitive data.
Download your complimentary copy of the report for expert insight on:
-Rapid evolution of phishing and infostealer malware that turn stolen credentials into profitable identity marketplaces
-Exploitation of unmonitored endpoints and shadow IT for ransomware deployment
-Strategic recommendations for building a Zero Trust identity architecture and implementing phish-resistant authentication
DM me to discover how Mowry International can help you reduce your exposure to ident
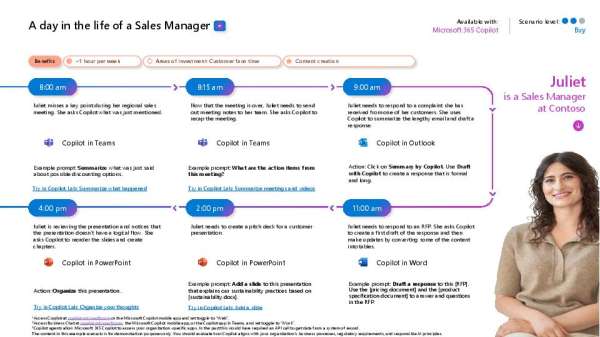
As a sales manager, you don’t just lead teams. You juggle meetings, respond to customer issues, and build presentations.
@Microsoft Copilot helps you do all that more efficiently. Give this infographic a read to see how Copilot supports productivity throughout the day. 📊