Similar Posts

Deepen and engage customers with AI
ByMBAAccelerate digital transformation that deepens engagement, predicts outcomes, and automates operations with #Microsoft Analytics and #AI. Subscribe to learn more!
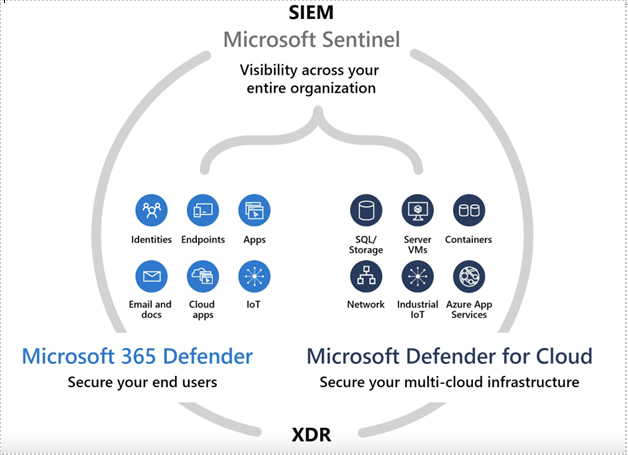
Social Message with Infographic
ByMBAPut the right tools and intelligence in the hands of the right people by combining SIEM and XDR with @Microsoft Sentinel and Microsoft 365 Defender. Tell us in the comments if you’d like to learn how from one of our experts.

The Right Way to AI
ByMBAWhen deploying AI, a little planning goes a long way. Here’s some advice from @Microsoft on steps you can take to a successful #AI adoption – which includes getting employees to embrace it. Read the article. 👀
Microsoft recognized as a Leader in the Forrester Wave: Data Security Platforms, Q1 2023
ByMBAWe are excited to share that Forrester ranked @Microsoft a Leader in its 2023 WaveTM for Data Security Platforms. Read this blog for a summary of the report — including why Microsoft earned the highest possible scores for data classification, data threat and risk visibility, Zero Trust integrations and other important criteria.

Transforming facilities management with Dynamics 365 at Microsoft
ByMBAMicrosoft real estate manages almost 600 buildings in more than 110 countries and regions around the world. When implementing change became too tedious and frustrating, the company adopted Dynamics 365 to unify dispersed management tools. At Mowry International, we can help your company use Dynamics 365 to streamline operations and cut out unnecessary management steps. Contact us today to learn more on how we can help.
Identity-Centric Threats: The New Reality
ByMBAThe way cybercriminals operate has fundamentally changed. The eSentire’s 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality” reveals how identity-based attacks have surged 156% since 2023, now representing nearly 60% of all confirmed threat cases.
Powered by Cybercrime-as-a-Service models, these attacks leverage Phishing-as-a-Service platforms like Tycoon2FA to bypass multi-factor authentication and gain rapid access to business email accounts and sensitive data.
Download your complimentary copy of the report for expert insight on:
-Rapid evolution of phishing and infostealer malware that turn stolen credentials into profitable identity marketplaces
-Exploitation of unmonitored endpoints and shadow IT for ransomware deployment
-Strategic recommendations for building a Zero Trust identity architecture and implementing phish-resistant authenticationDM me to discover how Mowry International can help you reduce your exposure to ident