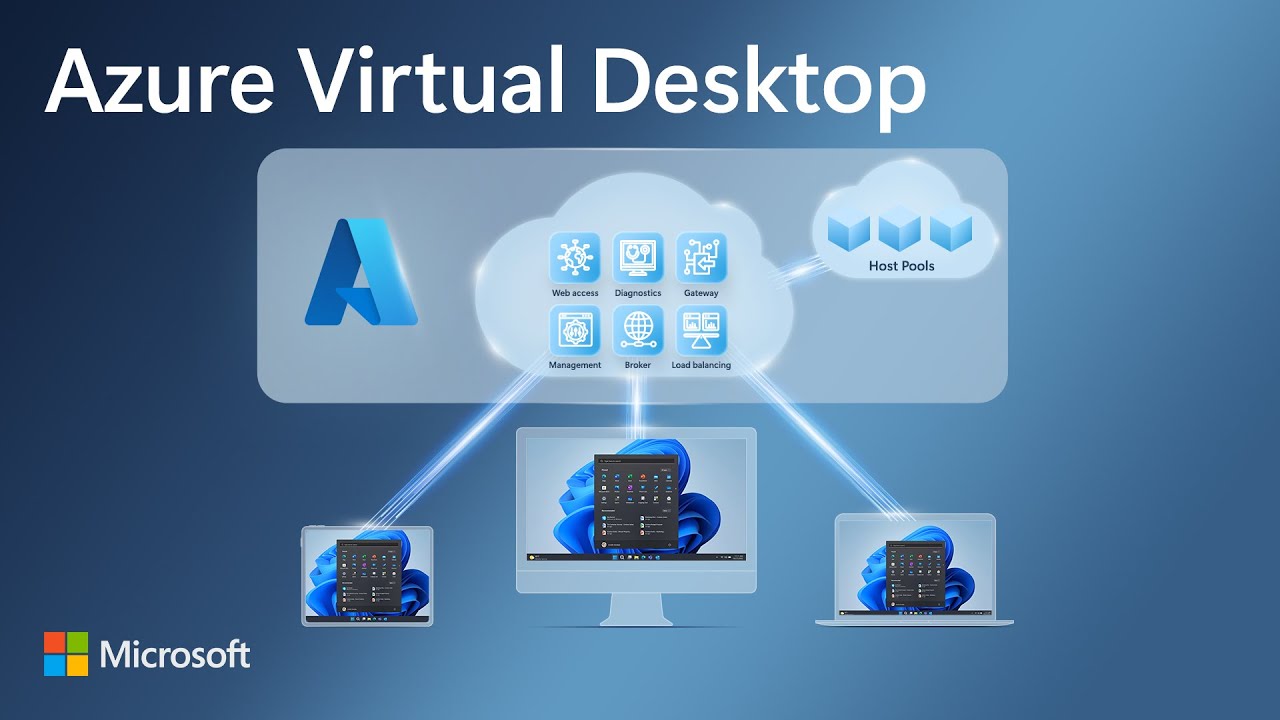
Azure Virtual Desktop Essentials: Intro and Full Tour
Azure Virtual Desktop works across devices and apps to deliver full-featured experiences for Windows, Mac, iOS and Android. The web client also allows you to access remote desktops and apps from almost any modern browser. This demo video takes you on a tour of Azure Virtual Desktop essentials. Watch the video for a walkthrough of what it is, how it works and configuration options.